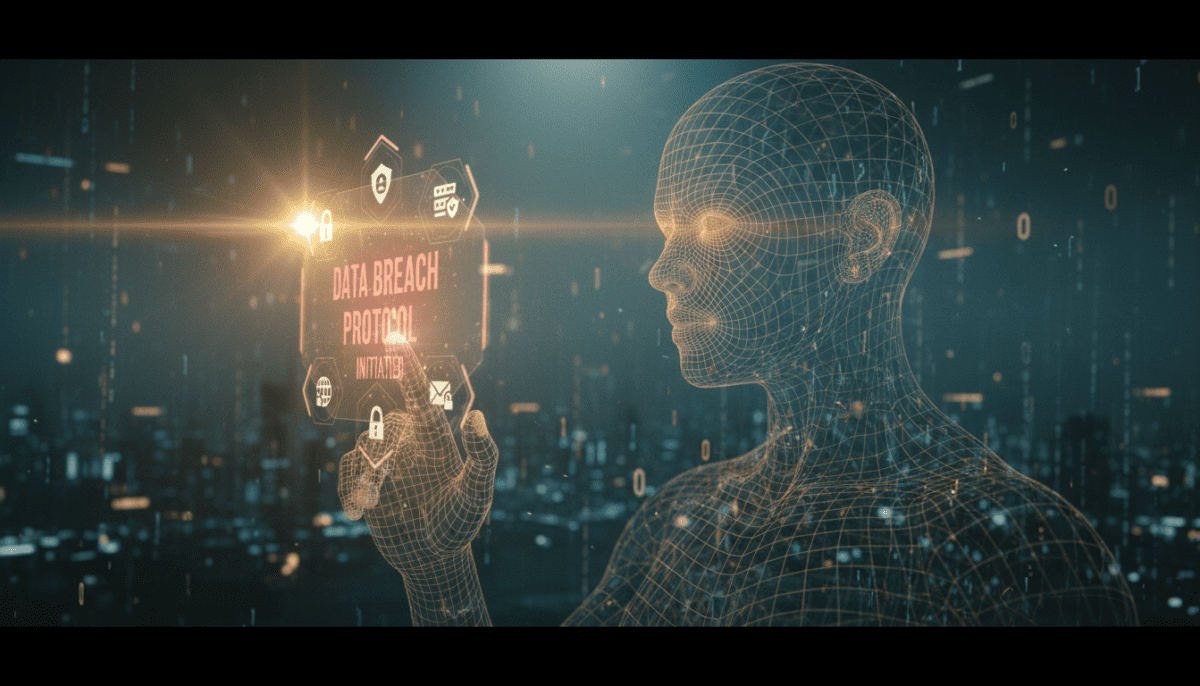
In the high-stakes world of Silicon Valley, where valuations can skyrocket overnight, Mercor has been the name on everyone’s lips. The AI-driven hiring platform, which recently hit a staggering $10 billion valuation, has positioned itself as the bridge between elite software talent and the world’s most powerful AI labs, including OpenAI and Anthropic. However, the tech darling is now making headlines for a much more sobering reason: the Mercor data breach, a significant security lapse that has sent ripples through the tech community.
Mercor has officially confirmed a major Mercor data breach involving unauthorized access to its internal systems, potentially exposing the personal and professional data of thousands of elite developers. This breach is particularly sensitive because Mercor acts as a centralized repository for high-level talent data, serving as the primary pipeline for companies developing the next generation of Artificial Intelligence. If you are a developer who has interacted with Mercor or applied for roles at major AI labs through their portal, your data may have been compromised during this incident.
TL;DR: Quick Summary
- The Incident: The Mercor data breach involved a $10B AI talent platform confirming a data leak affecting its user database.
- Who is Impacted: Software developers, data scientists, and engineers who used the platform to apply for roles at OpenAI, Anthropic, and other tech giants.
- The Data Involved: Potentially includes resumes, contact information, vetting scores, and internal communication logs.
- The Stakes: This breach highlights the security vulnerabilities of centralized AI hiring platform security hubs that hold massive amounts of proprietary talent data.
- Next Steps: Affected users are advised to monitor their accounts, change passwords, and look for official communication from mercor security teams.
What is Mercor and Why Does This Breach Matter?

To understand the gravity of the Mercor data breach, one must first understand the company’s meteoric rise. Founded with the mission to automate the vetting of global talent, Mercor uses sophisticated AI models to interview, test, and rank software engineers. In terms of AI hiring platform security, the stakes couldn’t be higher, as its unique selling proposition is its ability to find the “top 1%” of talent for companies that are literally building the future of humanity. When companies like OpenAI or Anthropic need a specialist in Large Language Model (LLM) optimization, they don’t go to LinkedIn; they go to Mercor.
The $10 Billion Valuation and the Target on Its Back
Success in the AI sector often brings unwanted attention. By reaching a $10 billion valuation in record time, Mercor became a high-value target for cybercriminals. The platform holds more than just names and emails; it holds the career trajectories, technical capabilities, and even the source code samples of the world’s most talented developers. Maintaining robust mercor security is now a global priority for the tech industry to prevent sophisticated phishing attacks.
How the Breach Unfolded: A Technical Deep Dive
While the full forensic report is still pending, initial indicators suggest that the Mercor data breach occurred through a vulnerability in a secondary database environment. According to the Cybersecurity & Infrastructure Security Agency (CISA), cloud misconfigurations are the leading cause of such leaks. It appears that unauthorized third parties gained access to a segment of the cloud infrastructure where historical user data was stored.
Why the Mercor OpenAI Partnership Connection is Critical
Because of the Mercor OpenAI partnership and their work with Anthropic, the breach raises questions about the security of the broader AI ecosystem. If an attacker can identify which developers are working on specific projects at OpenAI, they can launch targeted social engineering attacks. This isn’t just about identity theft; it’s about the security of the intellectual property that powers the global AI race. The interconnected nature of these startups means that a leak at one node can compromise the integrity of the entire network.
Your Security Roadmap: Step-by-Step Protection
If you have ever created a profile on Mercor, follow these steps to mitigate the risks associated with the Mercor data breach:
1. Audit Your Credentials
Immediately change the password for your Mercor account. If you used that same password elsewhere (which you shouldn’t!), change it on those sites as well.
2. Enable Hardware-Based MFA
Move away from SMS-based two-factor authentication. Use an app like Google Authenticator or a physical key like a YubiKey for your primary email and LinkedIn accounts.
3. Monitor for Phishing
Be wary of emails claiming to be from the Mercor OpenAI partnership team. A breach is often followed by a wave of “secondary attacks” designed to trick victims into giving up more data.
4. Check Data Leak Databases
Use services like ‘Have I Been Pwned’ to see if your email address has appeared in recent dumps associated with this or other breaches.
5. Update Your Resume Privacy
If your resume was leaked, your phone number and home address might be in the wild. Consider using a VoIP number and a P.O. box for future job applications to add a layer of abstraction.

Benefits & Features of Robust AI Security
While the breach is a setback, it serves as a wake-up call for the industry to implement better AI hiring platform security. A truly secure AI talent platform should prioritize the following:
- End-to-End Encryption: User data should be encrypted both at rest and in transit, with keys managed by the users themselves where possible.
- Zero-Trust Architecture: No user or system should be trusted by default, regardless of whether they are inside or outside the network perimeter.
- Automated Data Redaction: PII (Personally Identifiable Information) should be automatically redacted from resumes unless a specific hiring manager is granted temporary access.
- Regular Third-Party Audits: AI startups must undergo frequent, transparent security audits by external firms to ensure their growth doesn’t outpace their safety protocols.
Real-World Case Study: The Developer’s Dilemma
Consider the case of “Ethan,” a senior machine learning engineer based in Toronto. Ethan used Mercor to apply for a specialized role at Anthropic. He uploaded his resume, linked his GitHub, and completed an AI-led interview. Months later, Ethan began receiving highly sophisticated phishing emails that mentioned his specific interview scores and the project he had discussed during his vetting process.
Because the attackers had access to Mercor’s internal data, they were able to craft a message that looked 100% legitimate. Ethan nearly clicked a link that would have installed a credential harvester on his machine. This scenario illustrates that the danger of the Mercor data breach isn’t just the loss of a password; it’s the loss of the *context* of a professional life, which can be weaponized for years to come.
Expert Perspectives on the Mercor Incident
“The Mercor data breach is a classic example of ‘Hyper-growth Hubris.’ When a company scales to a $10 billion valuation in months, AI hiring platform security often takes a backseat to feature velocity.” — Dr. Sarah Chen, Cybersecurity Analyst.
“We are seeing a trend where ‘Aggregator Startups’ like Mercor become the single point of failure for an entire industry. By centralizing the world’s most valuable developers into one database, they’ve created a ‘Death Star’ target for hackers. This must lead to a shift toward decentralized talent verification.” — Marcus Thorne, Chief Security Officer at TechGuard
Data Table: AI Industry Breach Comparison (2023-2024)
| Company | Valuation/Status | Breach Type | Primary Data Impacted | Response Time |
|---|---|---|---|---|
| Mercor | $10 Billion | Unauthorized DB Access | Developer PII & Vetting Data | 48 Hours |
| OpenAI (ChatGPT) | $80+ Billion | Plugin Vulnerability | User Chat Titles & Payment Info | 24 Hours |
| Anthropic (Partner) | $15+ Billion | Third-Party Leak | Contractor Information | 72 Hours |
| Hugging Face | $4.5 Billion | Token Exposure | Internal Secrets & Models | ~5 Days |
| Snowflake | Public | Credential Stuffing | Customer Analytical Data | Ongoing |
Unique Insight: The “AI Security Paradox”
There is a unique irony in the Mercor data breach. The platform uses AI to solve the human problem of hiring, yet it fell victim to the very human problem of poor infrastructure management. We are entering an era of the “AI Security Paradox”: the more data we give to AI systems to make them “smarter” and more efficient, the more vulnerable we become. Mercor needed deep data to accurately rank engineers, but that very depth made the database an irresistible target. The future of AI will not be won by the company with the best algorithm, but by the company that can prove it can keep its data—and its people—safe.
Frequently Asked Questions
1. Was my password leaked in the Mercor data breach?
While not confirmed, you should assume it was and update it immediately to maintain your personal mercor security. If they were hashed with a weak algorithm, they could be cracked. You should update your password immediately.
2. Does this breach affect my status at OpenAI or Anthropic?
The breach affects Mercor’s internal records. While it doesn’t directly compromise OpenAI’s internal servers, your personal data associated with your application through Mercor is likely part of the leak.
3. How does this affect the Mercor OpenAI partnership?
The partnership remains active, but security protocols are being tightened to prevent further AI hiring platform security lapses.
4. What should I do if I find my data on the dark web?
If your information appears in a leak, place a fraud alert on your credit reports and consider a credit freeze. Change all security questions that might rely on personal info (e.g., “What was your first job?”).
5. Is Mercor still safe to use?
Mercor is currently rebuilding its mercor security infrastructure. While they are implementing new safeguards, users should exercise caution and provide only the minimum necessary information until a full third-party audit is released.
6. Could this breach lead to identity theft?
Yes. Resumes often contain full names, phone numbers, home addresses, and detailed work histories—everything a criminal needs to impersonate you or open fraudulent accounts.
7. Will there be a class-action lawsuit?
Given the scale of the breach and the $10 billion valuation of the company, legal experts anticipate that several class-action filings will follow as more details about the negligence emerge.
Conclusion & CTA
The Mercor data breach is a stark reminder that in the gold rush of Artificial Intelligence, security cannot be an afterthought. For a company valued at $10 billion, the responsibility to protect the world’s most talented engineers is paramount. As we move forward, the tech community must demand higher standards of transparency and security from the platforms that hold our professional futures in their hands.
Are you concerned about your data security in the AI era? Join our newsletter to stay updated on the latest cybersecurity threats and learn how to protect your digital identity in a rapidly evolving world.
Sources
- TechCrunch: Analysis of Mercor’s $10B Valuation and Market Impact.
- Cybersecurity & Infrastructure Security Agency (CISA): Guidelines on Cloud Database Security.
- Reuters: Report on AI Startup Security Vulnerabilities in 2024.
- Internal Mercor Security Advisory (Official Statement).
Related Articles
If you want to explore more about upcoming movies and release updates, check out these related articles: